Network Topologies and Functions
This lesson is all about fundamentals of computer networking and we describe a list of common components of a typical small network and see how we can lay them out in network diagrams. Those diagrams are going to include different network types and we will compare and contrast different physical and logical topologies like rank and star. The network is all about transporting applications, and so we will describe different methods of connecting to the Internet for a distributor approach to those applications.
What is a network? Networking basics
The first philosophical question of the day is: what is a network? Well, a network is nothing more than a collection of connected devices and end points and end systems with the purposes of exchanging and sharing information.
Now, today the network is a collection of devices and end systems, but those end systems include almost anything, not only computers, servers, but also telephones and cell phones and industry-automation machines that will now be involved in the exchange of information. That means we are exchanging not only data or traditional data in the form of files and other components, but also voice and video and multimedia collaboration. Another important piece is the scope of the network. If you think of the Internet, then there are networks everywhere. You also can think of the mobile user working from home, being connected and networked. The hierarchy is completed with teleworkers, home offices, branch offices, headquarters, and again, the Internet as a global network that interconnects us all.
Common Physical Components of a Network
Today’s network follow a hierarchy that kind of resembles human interaction and human organizations, so as you have people living in houses which comprise streets, which then are grouped into cities, and then from there to county, states, countries, etc., you also have PCs that are interconnected by switches, which in turn are interconnected by routers. As you look at the physical connection between these devices that form the hierarchy, you find the major components. So PCs are end systems; but again, IP phones are also end systems, and automation machines are end systems. Soon enough, your coffee maker will be an end system. Those end systems will be interconnected by switches, which provide the network attachment plus intelligent switching of information. In that interaction, you will see cable or wired and wireless media to connect the machines into the switch. You will also see components like the network interface card to provide networking to the end system, and also connecters to connect the media into the interface card. Routers will be there to connect network of switches and to provide the best path from network to network.
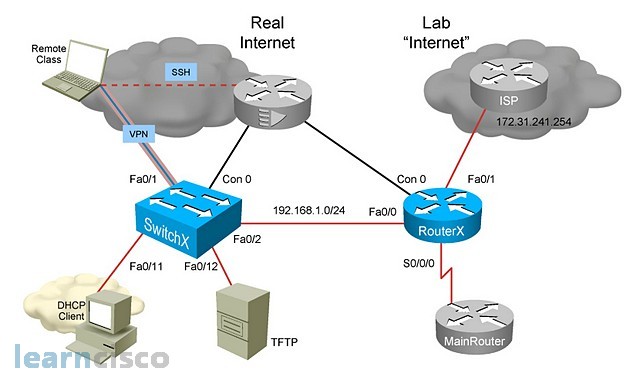
Interpreting a Network Diagram. Cisco networking
In designing, understanding, troubleshooting, and documenting our networks, we typically use network diagrams. These diagrams will typically contain as much information as we can without making them cluttered and useless. You typically also have different types of diagrams; physical topologies, for example, that will contain the physical connections between devices and information at the physical level. You also find logical diagrams that contain things like TCP/IP information, but you can also have network diagrams that include traffic flows, management information for troubleshooting purposes, etc. You may want to use consistent icons and terminology to build your diagrams. For example, here we have switches that are represented with that icon with the four arrows. Routers are typically round in this type of diagram, but they still contain the four arrows. You may use a solid straight line for Ethernet connections, but the flash for serial connections. Perhaps the icons are not important as much as the consistency of using similar icons for similar functions, and the same icon for the same device all the time. For example, the cloud in this instance is not really, or does not really, represent a rainy day; it is simply a network that may be out of scope, or outside of our administrative scope, and it has a series of devices behind it. But, that is transparent to us. We just want to represent a generic network. Also notice the use of text to identify IP addresses, interfaces, and management protocols.
Resource-Sharing Functions and Benefits
Networks are there to allow us to efficiently and effectively share information, share resources, and make us more productive. And by “us” I mean both individuals, organizations, countries, and so on. We may want to share data and applications, and again, by applications we mean the typical and traditional file or print job, but also multimedia voice, video, and so on. We may also want to centralize resources and have the resource only once instead of duplicating it across or among multiple users. So, we can have cameras connected to the network as input devices and share that camera across multiple users. Also, output devices like printers, network storage will also be there, backup devices, so we do not have to back up locally on each machine. We backup on the network and that resource is shared across multiple users. Those economies of scale should make us not only more productive but should also decrease costs and allow us to interact in a cost-effective manner. They also allow us to think transparently of network services. The physical location is no longer important. The network storage could be connected right next to us on the network or it could be in China, accessible via public networks like the Internet.
An impressive number of applications become available to us. However, some of them are commonly used, like email in the form of Outlook, or even “public” email like Yahoo!, Google, and so on. Web browsers allow us to open a window into the world and access a multitude of applications via this universal client. Instant messaging, collaboration databases become readily available, and these are examples of, perhaps, vendors and providers in real life of these services and applications.
Impact of User Applications
We can also categorize applications based on their impact to the network; in other words, how much information they send to the network and how much congestion they cause in the network. But, by the same token, we can also categorize them in terms of how they are impacted by the network. So, for example, bulk transfers and file tranfers like FTP and TFTP will typically add some more information to the network and send what they call packets into the network in high volumes. However, they may not be affected by network congestion to a big degree. If a file gets there a few seconds later, that may not be important or may not have an effect on the user experience. On the other hand, we have real-time applications, which may send fewer packets into the network, but be affected by network congestion to a big degree. End-to-end latency will hurt voice and make it have less quality. Right in the middle, we have interactive applications that will have an impact on user experience, depending on how fast or slow they go through the network, but may not be an issue depending on the type of application. Examples: inventory increase database updates, etc. It is important to understand, though, that all three types of applications will be in the network, and so it becomes the job of a function called quality of service, or QoS, to define that management of injustice. We will have limited network resources. And still, we have to allow all three applications into the network with different degrees of resistance to network conditions and different requirements.
Characteristics of a Network
With that in mind, we should design our networks using certain guidelines according to certain parameters. Some of those parameters are listed here: Speed and bandwidth are key especially knowing that we are going to have bandwidth hungry applications like video and multimedia collaboration in our networks. We do nothing by having a high-speed connection if that connection goes down all the time, so reliability is something we have to build into our networks. Some physical topologies may be more reliable than others. Some network elements may have a history of reliability problems while others do not. This leads to availability. Some services will require 100 percent, 24×7 by 365-type availability, while some others may not require that much. Typically, reliability is measured as percentage of uptime throughout a year, and so, some critical services may contain the five 9s: 99.999% uptime. This is tough to accomplish and it has certain requirements in terms of how you design the network. Security is also a critical factor as you build availability and reliability into the network, and as services contain more private customer information and mission-critical information from companies; protecting it is going to be key. All of these things are laid out in a network topology, but, perhaps, one of the most important factors, especially in the commercial realm, is cost. We will probably not be able to provide all parameters at 100 percent. This is going to be constrained by our budget and the cost of the technology.
Physical Topology Categories. Types of network
In networking, there are two types of topologies: the physical topology and the logical topology. Physical topologies define the cabling and the type of physical connection and the arrangements of those physical connections. The logical topology will be more of a definition of how data and traffic flows through the physical topology. It will contain logical paths, and not necessarily the physical path. These are examples of physical topologies, and they have been historically linked to the type of cabling we use to build the physical topology. For example, twisted pair versus coaxial versus fiber. In early bus topologies, devices would be connected or cabled together in a line using coaxial cable. This would result in a shared environment in terms of bandwidth. In a ring topology, machines would be cabled to each other, where the first machine and the last machine would complete the loop or the ring. A failed link would affect the ring and connectivity, and would cause longer roundtrip times. And that is why some people designed dual rings in the form of dual attachments between machines. In the star topology, a central device would connect the other devices and provide connectivity between them. And this resolved some of the issues in terms of reliability with the ring topologies. Star topologies typically use twisted-pair cables.
Logical Topologies
The logical topology, again, is the definition of how signals and information travel from point to point within the network. You may see a different logical topology then the physical topology, although they could be the same. For example, in a physical bus. Also, signals will use a logical line to travel from one point to the other. However, you may have a physical star like that. And still, machines are interconnected as if they were in the same cable. And so, the logical topology would be a logical bus. This is the case for Ethernet, and this is by far the most common architecture and physical logical topology in LAN scenarios in today’s networks.
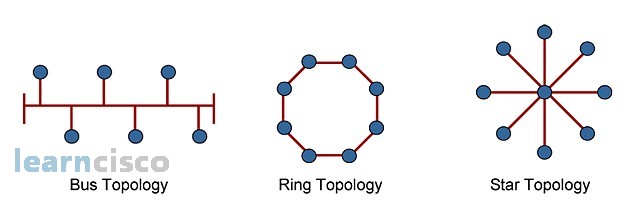
Bus Topology
In a physical bus topology, machines are effectively connected to a single cable. This is typically using coaxial cable. Termination at the end of that cable is important to prevent signals from bouncing back into the cable and causing network errors. Early local area networks would use this topology, but this is mostly seen in Internet access provided by cable companies nowadays. If you think of all devices being able to speak at the same time, then you will require another protocol or another method of access to the cable to prevent collisions and prevent network errors.
Star Topology
The physical star topology uses that central device to connect all other devices. In typical LANs, this device is a hub or a switch, and all transmissions go through that central point. Although, this improves reliability because the failure of one of those links would only affect that machine and not the rest of the network. Failure of the switch would represent a single point of failure and affect all of the network. That is why, if that is an issue and requirement, then some redundancy needs to be built into this topology.
Extended-Star Topology
The redundancy levels can be accomplished by following different strategies. For example, you could create more branches in the topology. In this example, that switch failing would only affect those three devices and not the rest of the network. You could also think about dual central switches and dual connections between each machine and the central switches. If one of the central switches goes down, then the other one will take over and allow for connectivity.
Ring Topology
In a ring topology, all devices are connected to each other in the form of a loop or ring; this is still different than a bus topology, although it looks like one or may look like one. Because they are not connected to a single line or cable, they are connected to each other, and those are different cables right there. Signals travel around the ring, sometimes in only one direction. Failure of one machine will affect the ring completely, representing a single point of failure, so you either have two-way transmissions or go to a dual ring for more redundancy and availability. Ring topologies can be in the form of a physical topology, but also logical topologies. For example, token ring is a physical star, typically, but with the use of a token, the machines will form a logical ring in terms of transmission of information.
Dual-Ring Topology
In a single ring, a failure of link or device will affect the whole ring. That is why we build redundancy. Then, you can allow for transmissions one way through one ring and building a second ring transmission the other way. This is better in terms of availability and reliability, but it goes at the expense of more cost in terms of connections, cabling, and links in general.
Full-Mesh Topology
The ultimate connectivity option is a full mesh. In this topology, all devices are connected to one another, resulting in the highest levels of redundancy and fault tolerance. This is expensive to implement though, and it is typically seen in WAN environments in connectivity between branch offices and central locations. There is no single point of failure, but it will still be sometimes too expensive to implement, and that is why there are other options that include partial mesh.
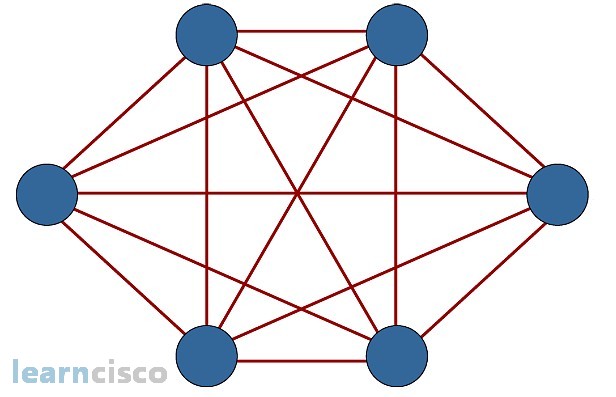
Partial-Mesh Topology
The partial mesh is a trade-off between fault tolerance and cost. You will probably pick and choose the most critical branches, or the most critical devices, and build more links and more redundancy to them while leaving the appropriate levels of redundancy for the less critical nodes. Most of the time, the defining factor here is cost and budget.
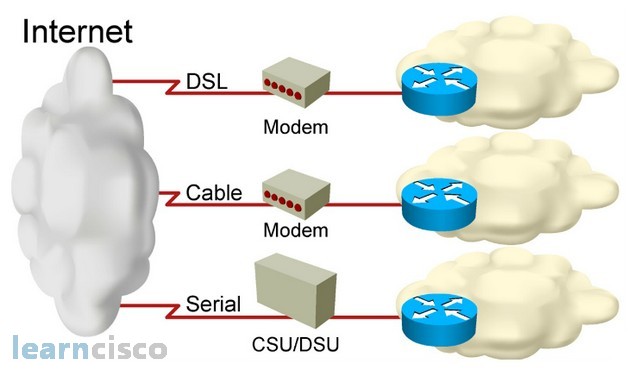
Connecting to the Internet
Connections to the Internet deserve special attention, since this is the public network that allows us global connectivity at a lower cost. Three common options are listed here. DSL will use existing telephone facilities of service providers to allow for data connectivity. Cable companies also have offerings that include Internet connectivity and IP traffic, and finally, the more traditional serial connections, which are typically related to TDM-type networks or time division multiplexing-type networks using CSU/DSUs for connectivity into the service provider network.